Security considerations for BI tools: Delving into the importance of safeguarding your data and systems, this introduction provides a captivating overview of the potential risks and best practices associated with BI tools security.
In today’s digital landscape, protecting sensitive information has never been more critical. As businesses rely on BI tools to make informed decisions, ensuring the security of these tools is paramount to prevent data breaches and unauthorized access.
Importance of Security Considerations for BI Tools

When it comes to using Business Intelligence (BI) tools, ensuring security considerations are in place is paramount. These tools are designed to collect, analyze, and visualize sensitive data that can have a significant impact on a business. Without proper security measures, this valuable information becomes vulnerable to unauthorized access, manipulation, or theft.
Potential Risks of Neglecting Security in BI Tool Implementations
Implementing BI tools without prioritizing security can lead to various risks and consequences. One of the major risks is the exposure of confidential business data to unauthorized individuals. This can result in data breaches, financial losses, damage to reputation, and legal implications for the organization. Neglecting security measures can also lead to data corruption, loss of customer trust, and regulatory compliance issues.
Examples of Security Breaches Due to Inadequate Security Measures in BI Tools
Several high-profile security breaches have occurred in recent years due to inadequate security measures in BI tools. One notable example is the Equifax data breach in 2017, where hackers exploited vulnerabilities in the company’s BI platform to gain access to sensitive personal information of millions of customers. Another example is the Marriott data breach in 2018, where unauthorized access to the BI system led to the exposure of customer data, including payment card information.
These examples highlight the real-world consequences of neglecting security considerations in BI tool implementations. Organizations must prioritize security to safeguard their data, protect their reputation, and maintain the trust of their customers.
Common Security Risks in BI Tools: Security Considerations For BI Tools
Business Intelligence (BI) tools are essential for extracting insights from data, but they also come with their own set of security risks that organizations need to be aware of. Let’s explore some of the common security risks associated with BI tools.
Data Leakage
One of the primary security risks in BI tools is data leakage, where sensitive information is unintentionally exposed to unauthorized users. This can occur through misconfigured access controls, inadequate encryption, or unauthorized data exports.
Injection Attacks
BI tools that allow users to input custom queries or scripts are susceptible to injection attacks, such as SQL injection. Hackers can exploit these vulnerabilities to manipulate the database and gain unauthorized access to sensitive data.
Insecure Authentication
Weak authentication mechanisms in BI tools can lead to unauthorized access to sensitive information. This can occur through weak passwords, lack of multi-factor authentication, or inadequate user access controls.
When it comes to utilizing business intelligence in the government and public sector, the benefits are immense. From improving decision-making processes to enhancing operational efficiency, BI plays a crucial role. Organizations can leverage data analytics to identify trends, monitor performance, and ultimately drive better outcomes.
To learn more about BI for government and public sector, check out this insightful article on BI for government and public sector.
Insufficient Data Encryption
Another common security risk in BI tools is the lack of proper data encryption during transmission and storage. Without adequate encryption protocols in place, data can be intercepted and compromised by malicious actors.
Third-Party Integrations
Integrating BI tools with third-party applications or services can introduce additional security risks. Vulnerabilities in third-party software or APIs can be exploited to gain access to the BI tool and the underlying data.
When it comes to utilizing Business Intelligence (BI) in the government and public sector, there are unique challenges and opportunities to consider. From improving decision-making processes to enhancing operational efficiency, BI can play a crucial role in transforming how public entities function.
To learn more about the benefits and applications of BI in government and public sector organizations, check out this insightful article on BI for government and public sector.
Best Practices for Securing BI Tools

When it comes to securing BI tools, implementing best practices is crucial to mitigate potential risks and protect sensitive data. Encryption, access control, and user authentication are key components in enhancing the security of BI tools.
Utilize Encryption for Data Security
Encryption plays a vital role in safeguarding data within BI tools. By encrypting data at rest and in transit, organizations can ensure that sensitive information remains secure and protected from unauthorized access. Implementing robust encryption protocols adds an extra layer of defense against potential threats and breaches.
Implement Strong Access Control Measures
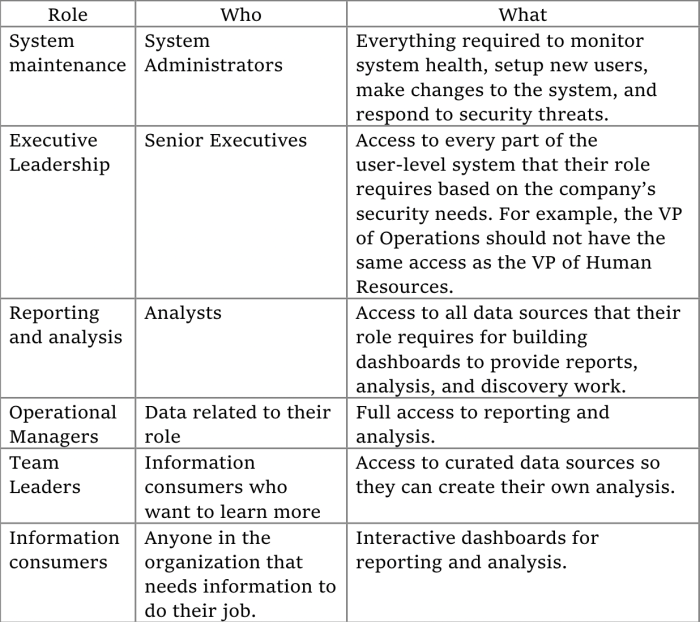
Access control is essential for maintaining the security of BI tools. By defining user roles and permissions, organizations can restrict access to sensitive data and ensure that only authorized personnel can view or manipulate information within the BI platform. Implementing least privilege access principles helps prevent data leakage and unauthorized data access.
Enforce User Authentication Protocols
User authentication is a critical aspect of BI tool security. By implementing multi-factor authentication and strong password policies, organizations can verify the identity of users accessing the BI platform. This helps prevent unauthorized access and ensures that only legitimate users can interact with sensitive data. Regularly reviewing and updating user credentials further strengthens the security posture of BI tools.
Compliance and Regulatory Requirements

When it comes to security considerations for BI tools, compliance with regulatory requirements such as GDPR, HIPAA, or PCI DSS plays a crucial role in ensuring data protection and privacy. These regulations dictate how organizations should handle sensitive information, including data accessed through BI tools.
Impact of Compliance Regulations
- GDPR: The General Data Protection Regulation (GDPR) mandates strict rules for protecting personal data of EU citizens. Organizations using BI tools must ensure that data processing is done securely and in compliance with GDPR to avoid hefty fines.
- HIPAA: The Health Insurance Portability and Accountability Act (HIPAA) governs the security and privacy of healthcare data. BI tools used in healthcare settings must adhere to HIPAA regulations to safeguard patient information.
- PCI DSS: The Payment Card Industry Data Security Standard (PCI DSS) Artikels security requirements for organizations handling credit card information. Compliance is essential for BI tools processing payment data to prevent data breaches.
Challenges in Meeting Regulatory Requirements
- Complexity: Compliance with multiple regulations can be challenging due to the intricate requirements and frequent updates to regulatory standards.
- Data Governance: Ensuring data governance practices align with regulatory mandates can be a daunting task, especially in organizations with large volumes of data.
- Resource Constraints: Limited resources and expertise in compliance management can hinder organizations from effectively meeting regulatory requirements.
Consequences of Non-Compliance, Security considerations for BI tools
- Legal Penalties: Non-compliance with regulatory requirements can result in severe legal consequences, including fines, lawsuits, and reputational damage for organizations using BI tools.
- Data Breaches: Failure to comply with regulations increases the risk of data breaches, leading to potential financial loss, loss of customer trust, and regulatory sanctions.
- Lack of Trust: Organizations that do not prioritize compliance may face challenges in gaining the trust of customers, partners, and stakeholders, impacting their business relationships.
Final Conclusion
In conclusion, prioritizing security considerations for BI tools is not just a necessity but a strategic imperative in safeguarding your organization’s valuable data assets. By implementing best practices and staying compliant with regulations, you can effectively mitigate risks and protect your business from potential security threats.